The following article summarizes a multi-part series I’m writing on standing-up an open source Security Incident Response Platform. This platform allows for log retention and analysis, alert generation, IoC enrichment, and case management.
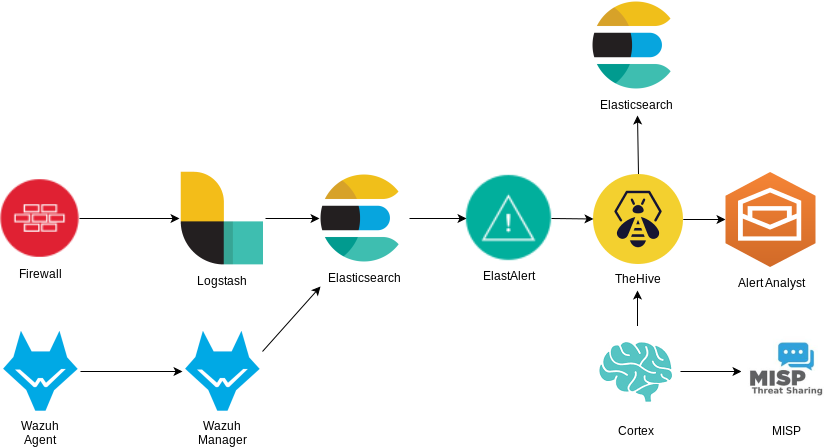
In the above flow chart, the Wazuh HIDS agent sends data back to the Wazuh Manager and Elasticsearch. From there, ElastAlert will watch for new events of interest and generate alerts inside TheHive. A workflow will then enrich the case with additional queries from the Cortex analyzers and MISP, resulting in either an automatic closure of the case or an escalation to an analyst.
Alerts are available for Analysts to claim and trigger enrichment through Cortex and MISP.
Please note that any endpoint service or agent that generates logs to feed into Elasticsearch can be used instead. A benefit of this system is that most components can be swapped out with alternatives.
Part 1 - Elasticsearch Installation
Part 2 - Wazuh Installation
Part 3 - MISP Deployment
Part 4 - TheHive & Cortex
Part 5 - ElastAlert
Part 6 - Case Management
Components
Wazuh
Wazuh is an open source security monitoring solution which collects and analyzes host security data. It is a fork of the older, better known OSSEC project.
The Wazuh server component integrates closely with Elasticsearch and Kibana while the agent is capable of many security related tasks such as log analysis, rootkit detection, listening port detection, and file integrity monitoring. For this project we’ll utilize these capabilities to generate alerts.
Elasticsearch
Elasticsearch will act as our log repository. It’s incredibly powerful and versitile, and when coupled with Logstash for log ingestion and Kibana for visualization, provides a robust platform for all types of data.
ElastAlert
ElastAlert is an open source project started by the engineers at Yelp to provide an alerting mechanism for Elasticsearch. It’s an independent project that doesn’t need to run on the same server. It simply queries Elasticsearch through the REST API and has numerous outputs to alert on a match. One of those outputs will feed the information into TheHive. This is how we distinguish the noise from the important events in the logs and generate alerts.
TheHive
TheHive describes itself as “A scalable, open source and free Security Incident Response Platform designed to make life easier for any information security practitioner dealing with security incidents that need to be investigated and acted upon swiftly”.
In essence it’s an alert management platform for managing an incident alert from creation to closure.
Cortex
Cortex is another software product from the same team as TheHive and complements that product with data enrichment. Cortex allows the use of “analyzers” (113 as of this writing) to gain additional information on the indicators already present in your logs. It allows the querying of third-party services on indicators such as IP, URL, and file hash, and will tag the alert with this additional information. No need to send a file hash manually to VirusTotal when an analyzer will automatically do it for you and tag the alert with the results.
MISP
MISP is an open source threat sharing platform maintained by CIRCL which, among many other uses, allows the operator to subscribe to threat intelligence feeds. These feeds can either be paid subscriptions or community maintained feeds from various organizations, and are our primary source of data enrichment.
In the rest of the series we’ll look at installing each component and configuring them to inter-operate. Then we’ll generate some alerts and manage a case from open to close. Stay tuned!